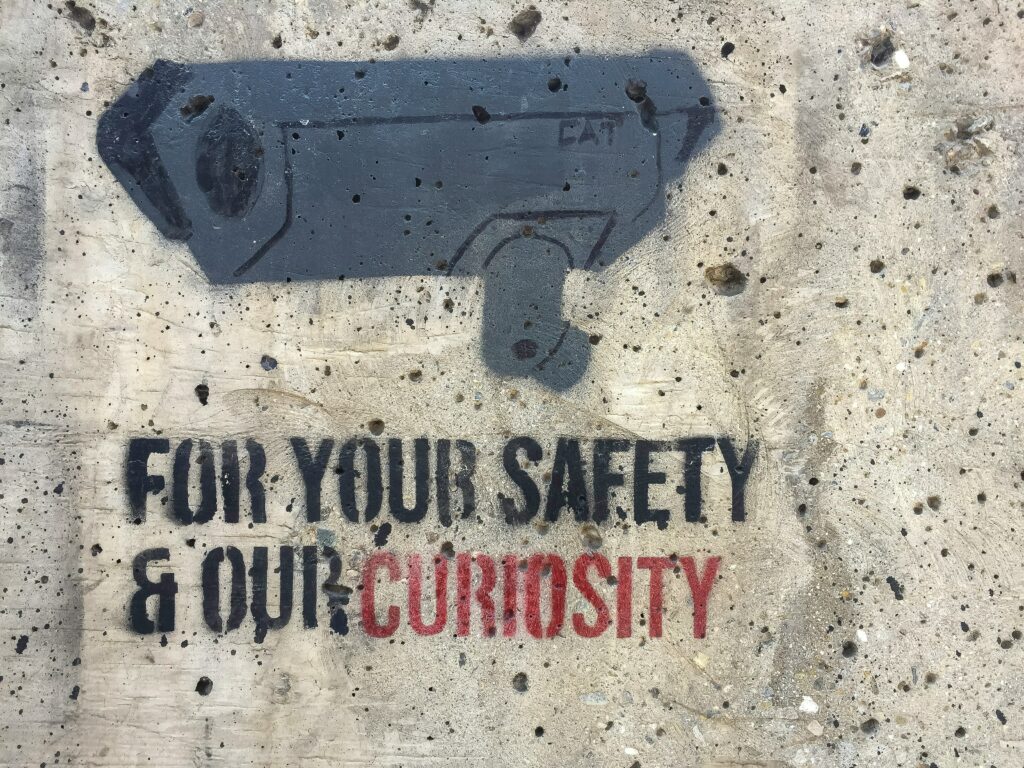
“If you’ve got nothing to hide, you’ve nothing to worry about.” Whenever there’s a discussion about privacy, this is the counter-argument that comes up. So, should you be worried about your privacy if you are not doing anything wrong? Let’s find out.
In this article, we will explore privacy in the age of digital surveillance. We will uncover some popular myths about privacy and help you understand why you should protect your privacy in the digital space.
To begin with, let’s clear the obvious misconception.

Yes. You have things to hide; everyone does. If not, would it be okay to share your private photos with strangers? Will you post your bank account information or your credit card statement on your Social media accounts? Would you be okay if your parents read your WhatsApp conversation with your partner?
No, right? So, we all have things to hide. The point is we all are conveniently ignoring that. Or there is a misconception that privacy is for bad people or criminals trying to run away from authorities. This is because people confuse privacy with secrecy. Privacy doesn’t mean anonymity; it means your right to protect your personal life from public scrutiny.
In the age of digital surveillance, we are trading our privacy for convenience. Convenience is the illness of modern society. It is the reason why most people ignore privacy.
Some argue that using Amazon’s Alexa to control things like AC and lights with voice commands is very convenient. Before IoT smart devices, nobody would have thought switching on an AC is such a big task.
Now, everything from toothbrushes to cars is connected to the internet, collecting a large amount of information daily. These devices know where we live, where we go, and if they have voice commands, they might even hear what we say, leaving behind numerous digital footprints.
Amazon’s Alexa has been notorious for mishandling the personal information of its users. In 2018, a German Amazon customer received 1,700 audio files from a stranger’s Echo device by mistake. This revealed enough details for the recipient to identify the device owner, including their name, location, and details about their girlfriend.
We are not being pessimistic about technology and the internet; we recognize their daily-life benefits. However, the concern is that the data collected doesn’t stay with the devices; it’s shared with data brokers, big companies, or government agencies.
Now, you may think, “I am just an average Joe; why would they be interested in me?” Well, they can use this data to manipulate you, influence your purchases, discriminate against you, or even control your personal life.
Remember the Cambridge Analytica scandal? It involved the British consulting firm and Facebook using the personal data of millions of Facebook users without their consent for political advertising in the US.
So, if you are trading off privacy for convenience, it could cause harm to you in different ways.

Social media has given everyone an opportunity to become a celebrity. People are navigating a world where sharing intimate aspects of their lives is not just a personal choice but a strategic move to gain attention, followers, and, ultimately, fame. A walk through their social media profiles reveals not only carefully curated content but also glimpses into their daily lives, relationships, and even personal challenges.
One of the driving forces behind this preference for celebrity status is the instant gratification and validation that social media provides. Likes, comments, and shares serve as tangible indicators of popularity and influence. The more personal and relatable the content, the higher the engagement and, subsequently, more fame and followers.
However, this tradeoff between privacy and fame is not without consequences. The exposure of their personal information on social media opens individuals up to scrutiny, criticism, and potential intrusion into their private lives.
It’s been over a decade since Edward Snowden leaked classified information from the NSA (National Security Agency) about their mass surveillance of Americans’ telephone records. Many major tech companies, including Microsoft, Google, Yahoo, Facebook, and Apple, were also involved in providing users’ data to the agency without their consent.
Initially, the NSA refused these allegations but later was forced to admit that they were spying on their own citizens. Furthermore, many NSA employees used these spy tools to spy on and stalk their spouses and ex-lovers.
Even after ten years, nothing has changed so far. Government agencies and tech companies continue to collect data on citizens and their customers. Now, with more connected devices we use daily, they have more means to collect personal information.
Surveillance, when unchecked or invasive, has the potential to significantly impact our lives in various negative ways. Here are several ways in which surveillance can have negative effects:
Loss of Privacy
When we are under constant surveillance by government agencies, corporations, or technologies, it affects our fundamental right to privacy by all means. The feeling of being constantly observed can lead to increased stress and anxiety as individuals struggle to maintain personal boundaries.
Influence Our Decisions
Digital surveillance gives more power to government agencies, as they’ll be aware of our personal lives and matters and influence our decisions and our votes, silencing us from raising dissenting voices, blackmailing, or even stalking us.
Corporate Surveillance
Corporates also love to monitor their employees. Many companies use different data surveillance tools and services to rate their employees with employability scores to determine employability, trustworthiness, loyalty, etc. They use personal information to predict the future behavior of their employees.
Blackmailing
When your private data is exposed or accessed by third parties, it can be used against you to blackmail. One awful scam that has spread globally involves finance apps offering “hassle-free” instant loans to users. Upon downloading these apps, individuals are prompted to share photos, self-declaration videos, and contacts as part of the supposed “verification processes.”
Subsequently, after granting the loan, these companies impose hefty interest rates. If a borrower struggles to repay the loan, the lenders resort to sending messages to all contacts in the borrower’s phone. Victims are then threatened to repay their loans with heavy interest rates. Shockingly, a BBC report reveals that 60 Indians have killed themselves after being abused and threatened by such loan apps.
Social Stigma and Discrimination
Surveillance data can be misinterpreted or selectively used to target specific groups or individuals. This can result in unfair profiling and discrimination based on characteristics such as race, religion, gender, or political beliefs.
For example, if someone visits a queer dating app, it collects personal data and identifiable information of that person. When this information is sold or leaked to the wrong hands, it can cause severe consequences.
This actually happened in Egypt when police and blackmailers used queer dating apps like Grindr, Hornet, and Growlr to find LGBTQ targets. Even though homosexuality wasn’t illegal in Egypt, they were humiliated in public.
You may think, what is the point of discussing privacy when it is already gone? But let’s be optimistic on this matter. There has been a recent wave towards privacy. We have seen many countries come up with data protection laws to protect the privacy rights of their citizens.
To protect personal data, the first thing you should do is to reduce your digital footprints. You should be aware of your privacy rights and know what data you share and who all have access to it.
Limit the app permissions, block browser cookies, and provide controlled access only. It is also ideal to use strong and unique passwords and update your passwords regularly. Additionally, you can use various privacy-focused tools and services like web browsers such as Firefox and Tor, search engines like DuckDuckGo, etc.
Other tools include password managers, ad-blockers, VPNs (Virtual Private Networks), encrypted messaging services, and open-source operating systems and applications.
Our privacy is ours to protect. We should demand strong data protection regulations and privacy rights to protect our privacy in the age of surveillance.
To Wrap Up
Privacy doesn’t mean anonymity. We all have the right to protect our personal data and protect our private life from surveillance and monitoring. We can still continue enjoying modern technology and social media networks while protecting our personal data.
The purpose of this article was to help you understand why you should protect your privacy, even if you believe you have nothing to hide.
To sum up, here’s a well-known quote that serves as a counterargument to the “I have nothing to hide” mindset:
“Ultimately, arguing that you don’t care about the right to privacy because you have nothing to hide is no different than saying you don’t care about free speech because you have nothing to say.” – Edward Snowden